Cyber threats can be scary, and for good reason. Malware can be lurking in a suspicious email your users get convinced to click. All it takes is one crack in the door of your network to let cybercriminals in.
A resilient security culture in your organization is your best bet for keeping you safe form a cyber attack.
Top Strategies to Mitigate Cyber Risks
Content by guest contributor Natalie Chan, Senior Risk Advisor, Waypoint Insurance
In today’s interconnected world, the threat of cyberattacks looms large over individuals and businesses alike. To safeguard sensitive data and maintain operational integrity, it is crucial to implement effective strategies to mitigate cyber risks. This high-level overview outlines key strategies to protect against cyber threats.
- Risk Assessment and Prioritization: Begin by identifying and categorizing your organization’s assets and potential vulnerabilities. Assess the impact and likelihood of various threats to prioritize resources effectively.
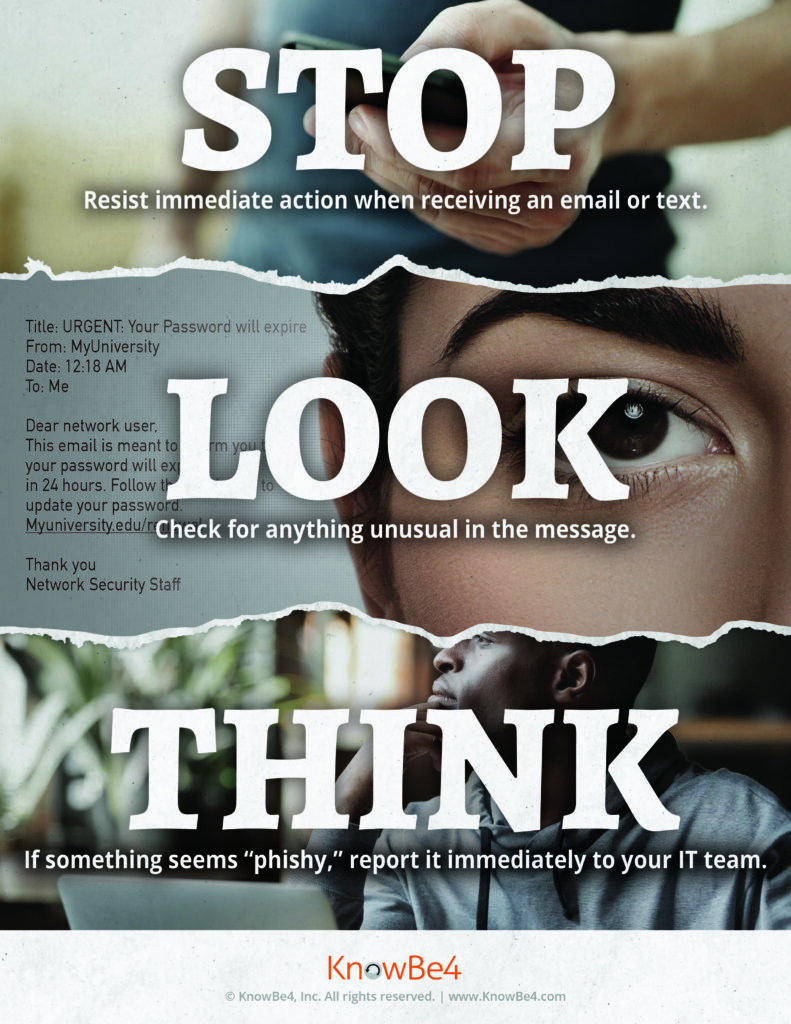
- Internal Cybersecurity policies and Training: Develop comprehensive cybersecurity policies and provide ongoing training to employees. Ensure this is part of the company’s culture where everyone is aware of best practices and understands their role in being vigilant.
- Access Control and Identity Management: Implement robust access controls and identify management systems to restrict access to sensitive data or systems. Use multi-factor authentication to enhance security.
- Regular patching and Updates: Keep all software, operating systems, and security tools up to date. Retire any end-of-life products-vulnerabilities in outdated software are prime targets for cyberattacks.
- Network Security: Employ firewalls, intrusion detection/prevention systems, and encryption to safeguard your network. Encrypt sensitive data both at rest and in transition.
- Backup and Recovery: Maintain regular backups of critical data and systems. Ensure backups are isolated form the network and routinely test data restoration process.
- Incident Response Plan: Develop a well-defined incident response plan that outlines how to detect, report, and respond to security incidents promptly. Regularly test and update the plan.
- Vendor Risk Management: Assess and monitor the cybersecurity practices of third-party vendors and partners. Ensure they meet your security standards.
- Cyber Insurance: Consider investing in cyber insurance to mitigate financial loss associated with data breaches and attacks.
In conclusion, cyber threats are constantly evolving at a speedy rate. Employing a multi-layered approach to cybersecurity, encompassing technology, policies, and a vigilant workforce, is essential to protect against threats. Regular evaluation and adaptation of these strategies will help organizations stay one step ahead to safeguard their valuable assets.
Additional Resources:
Video: Security Culture and You
Learning Module – When you report, we get stronger
Interactive Game – Danger Zone
We have a full kit of resources for Cybersecurity Awareness Month. If you would like them to share with your team, please contact Gillian at gcampbell@arbutusfinancial.com and she will send them to you.